This page provides an overview of the approach BioMedIT takes to security, and the security architecture in place to secure the platform and services. You can request access to the full policy for legitimate reasons by contacting BioMedIT.
BioMedIT Security Concept & Architecture
Security Challenges
BioMedIT exists in order to enable and empower safe research using personal health data, in order to support improved future healthcare. The use of personal data means that security must be a priority, but security in such an environment is not simple. The following sections set out the challenges faced in securing BioMedIT.
Respect data and data subjects
In supporting the research using personal health data, it is crucial to respect the data subjects who volunteered their personal data in support of research, as well as the data itself. All care must be taken to act within the bounds of the consent granted, and within national and other laws and regulations. This means being clear in identifying who has responsibility for data, and ensuring that storage, transmission, combination, use and export of data are legally permitted, ethical, and based in agreements. All stakeholders must contribute to this effort, as a failure to protect data subjects, through disclosure, misuse or other unauthorized behavior, would seriously damage the credibility of not only BioMedIT, but the broader mission of using personal health data to improve future medicine.
Balance usability and security to empower research
While all care must be taken to preserve the confidentiality, integrity and availability of sensitive data, it must also be usable for research. Much of the valuable data collected and mobilized by BioMedIT comes from a clinical context rather than a research context, where its use is very different to that in research. In order to generate new research insights, the data mobilized must be in a form usable by researchers, and researchers must be able to interact with the data in a useful way. Data must be accessible to current research practice, and allow for the innovation and creativity of creative research, as well as very well planned and structured data processing. BioMedIT must be able to allow innovative research while maintaining the security necessary to protect the rights and consent of data subjects.
Increase cohesion and facilitate federation
Delivering on the needs of research and of data subjects requires disparate groups to work together, and to find ways to build bridges between communities. At the level of data, this means building cohesion in formats and structures, and the move towards structured, curated data in data warehouses, using rich metadata and technologies such as graph data. Moving towards common data formats and structures opens up new opportunities for research, as well as opportunities for data reuse. For organizations this means finding transparent ways to collaborate in delivering services to research, which often require multiple organizations to federate in order to deliver them. This federation creates a complex system with many potential security vulnerabilities which must be effectively managed.
Informing and educating the community
Security and privacy are widely understood to be important, especially in the community supporting health research, but the majority of the community members are not well informed on the subject. While senior staff and legal specialists may understand the intricacies of risks, laws and agreements, most individual researchers do not. Threats to health research systems may result from those trying to compromise them, but as often will result from accidental actions result in incidents. All those involved require sufficient education and information to cope with these issues.
Create an elevated trust level
The collaboration and federation needed to deliver personal health data for research requires a set of trust relationships between stakeholders. The creation and maintenance of these relationships has been a major effort and achievement of BioMedIT to date. In particular trust between data subject and data providing organizations such as hospitals, and then between these data providers and research organizations. This trust is based on long term engagement, supported by national funders, but also relies on the security offered by BioMedIT. If security measures fail, apart from the specific incident and direct impact of it, this may undermine these trust relationships, and damage the overall pursuit of improved research and medical practice.
Security concept
Based on these security challenges and the overall goals of BioMedIT, we describe the BioMedIT security concept, summarized in the following diagram.
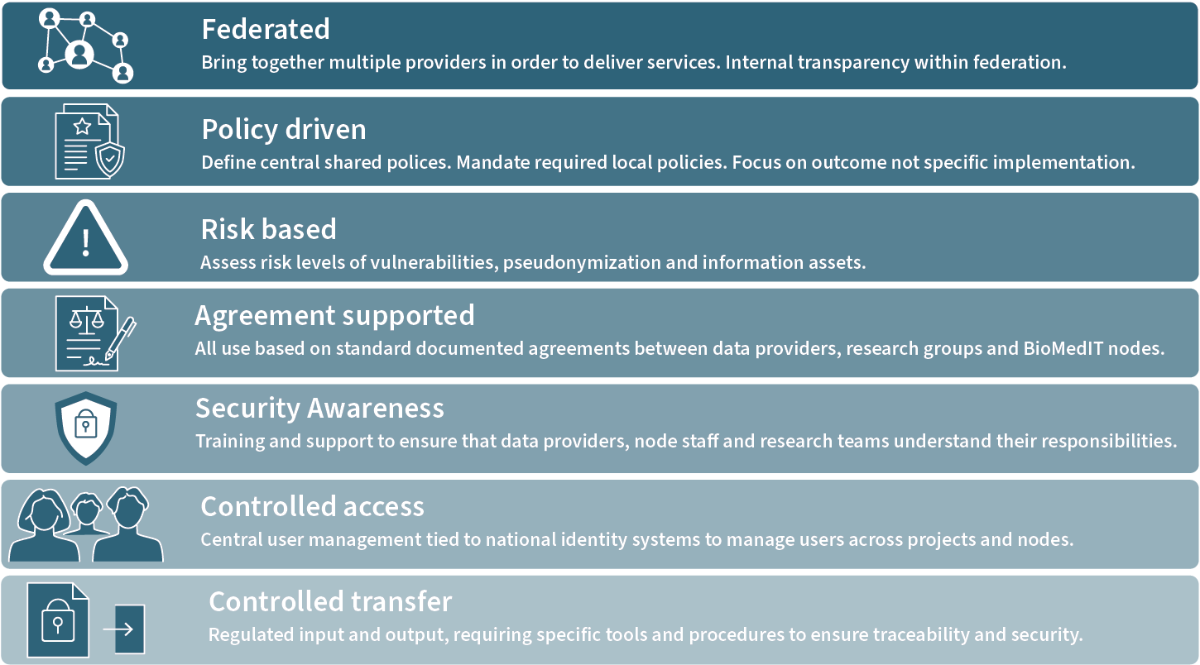
Federated
BioMedIT operates a federated, multi-stakeholder infrastructure and community. In the past, security in sensitive data processing has been maintained by restricting sensitive data to silos, which have included those in public organizations managing person data, such as hospitals, but also those in commercial organizations performing sensitive research. Mobilizing sensitive data for multi-center, multi-organization research projects involved going beyond these silos. There is no single overriding authority to enforce security over these collaborations and federations, except for legal regulation. Federated scenarios lack single central authority, and rather proceed through negotiation and mutual interest. In order to make this work, the BioMedIT community must address the challenges of federation and collaboration in delivering and consuming services.
First, the federated nature of the situation must be recognized, and the structure of the federation mutually understood. Within the BioMedIT sites delivering services (BioMedIT nodes and BioMedIT central) this implies a large degree of transparency in staff, policies and processes. In security, the sharing of security plans, and alignment of security policies, process and where possible, tools. With the data providers and research projects this means having clear lines of communication, and clearly expressed expectations on the rules governing behavior and the expected actions of each stakeholder.
Policy driven
Because BioMedIT operates in a federated manner, it is not possible to simply centrally determine and enforce security, whether in terms of organizational or technological measures. To address this, BioMedIT works in a policy driven way. Overall policies, including security policies, are agreed by the BioMedIT sites, and set out overall goals and requirements. Each site is then required to create and enforce its own local policies in order to implement the overall policy. This approach allows for cohesion in approach and outcome, but differences in specific and technical implementation. The overall, global policies are then public, and help build trust with other stakeholders. The specific local polices are not public, but the BioMedIT sites perform internal mutual review of local policies in order to ensure they are effective and harmonized.
Risk based
No system can be perfectly secure, and even a theoretically perfect system would become vulnerable due to technical change, changing risks and the need for perfect behavior, BioMedIT takes a position of Risk based assessment of security, privacy and other risks. Risks are assessed for various aspects, including security vulnerabilities, risks in pseudonymization of sensitive data, and risks associated with access, storage and transfer of information assets. For information assets, risks levels are defined and assigned to all assets. Risk level then governs how assets are handled, processed and disclosed where appropriate. A risk-based approach supports realistic assessment of threats and vulnerabilities, and avoids complacency based on an incorrect assumption of a perfect security model. It also better acknowledges the importance of correct behavior rather than purely technical measures in ensuring security.
Agreement supported
Engagement between BioMedIT sites and other stakeholders, especially data providers and research projects, is based on clear, signed agreements between organizations. These provide a legal basis for the processing of highly sensitive data, and also clarify roles and responsibilities, and the policies under which work is conducted. BioMedIT only allows access to and processing of sensitive data once agreements are signed. These agreements are generally based on templates provided by the BioMedIT community, checked with legal officers and compliant with national regulations. BioMedIT also provides legal and ethical support which assists with the negotiation and signing of agreements, and monitors their status to ensure that all transfer, storage and processing of data is permitted and supported by an agreement.
Security awareness
Because BioMedIT works on a policy driven and federated basis, security is not achieved solely through technical means and limitations. A significant contribution to the security of BioMedIT comes from the personal behavior of the stakeholders and participants in the system. As a result, it is key that participants in BioMedIT are aware of the security measures and limitations of the system, and what behavior is expected and legally required of them. To this end, BioMedIT provides basic information security awareness training on safe use of research data, and safe use of BioMedIT. Staff from research projects and data providers must pass this training prior to being gives access to secure systems. BioMedIT also supports skill development of staff at BioMedIT sites grow the overall level of security awareness in the community.
Controlled access
In accordance with the principles of information security, all access to BioMedIT systems and data are controlled, and is based on identified Risk levels. For BioMedIT sites, staff are carefully screened and must undergo security awareness training. All external use, including by research projects or data providers, is based on signed legal agreements. BioMedIT confirms organizational affiliations of individuals, and stakeholders are required to maintain and update the lists of valid users under their organizations.
Controlled transfer
Transfer of data into and out of the BioMedIT infrastructure is tightly controlled. Data may only be imported through permitted means must be properly logged, and for high risk data such as research data, specialist transfer tools and considerable encryption is required, and such transfer must be supported by a legal agreement. Export of data is equally controlled, and only allowed with logging and using permitted technical mechanisms. BioMedIT provides support for pseudonymization and research projects ensure only aggregated results are exported for publication. Export of sensitive, high-risk data is only possible with prior agreement of data providers.
General Security Architecture
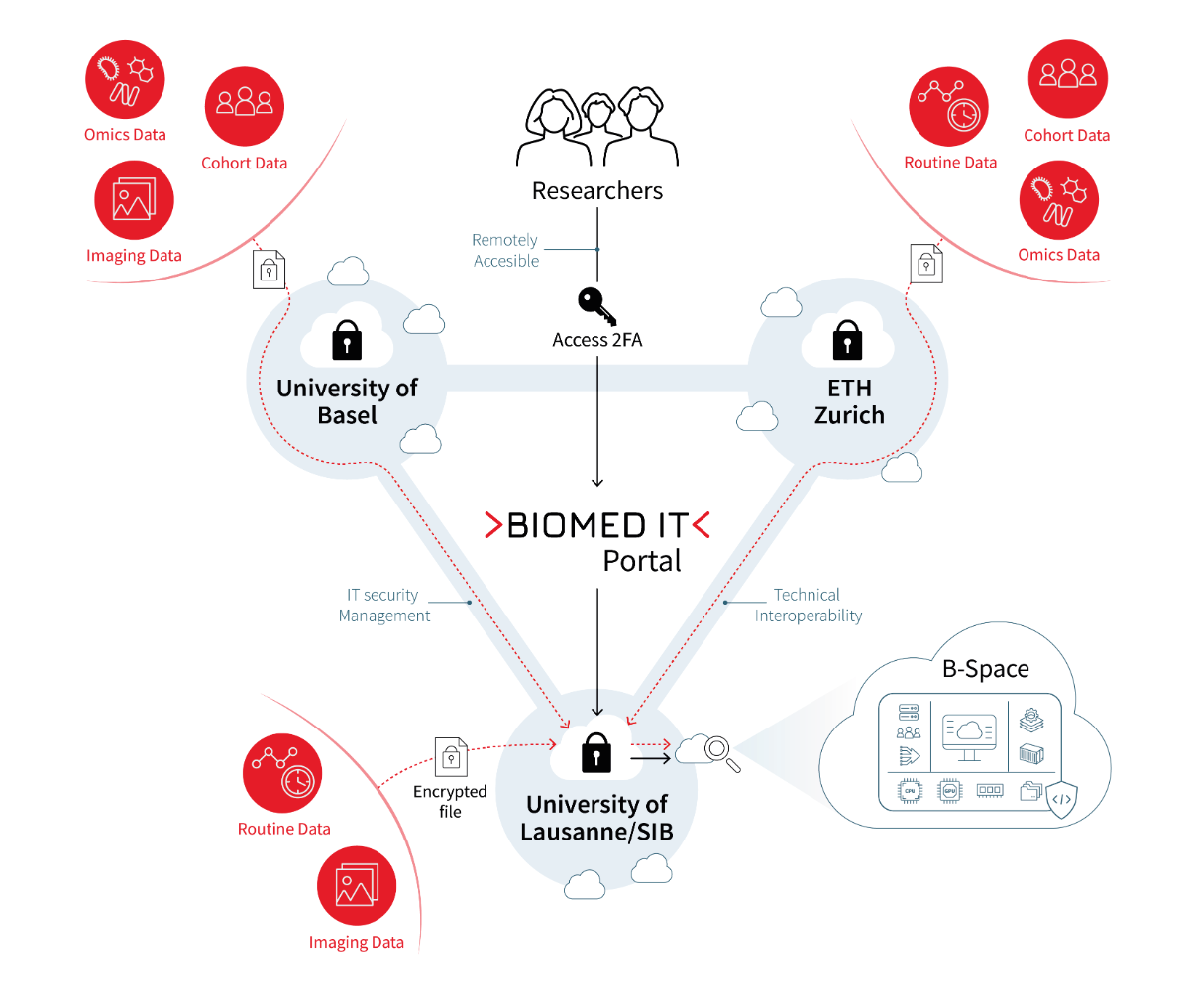
BioMedIT Network
The BioMedIT network spans across scientific IT competence centers of three major Swiss universities: sciCORE, operated by University of Basel, SENSA, operated by University of Lausanne in collaboration with the Swiss Institute of Bioinformatics (SIB) and SIS, operated by ETH Zurich. The network provides researchers access to cutting edge cloud computing, virtualization, compute accelerators (GPUs), big data storage and federation technologies where data regarded sensitive as per law could be processed in a secure, ethical and legal manner. The network accepts secure data transfers from data providers such as Swiss hospitals and research organizations in encrypted format where it can be safely accessed by recipient researchers from bonafide Swiss research institutions.
The three BioMedIT sites (nodes) form a shared security zone, based on their shared security policy and coordination. Projects from research consortia or single researchers wishing to use sensitive data are set up as research projects on one of the nodes in a BioMedIT project-specific environment, called a 'B-Space'. Research groups can access their B-spaces via the BioMedIT Portal, where they can manage users and encryption keys, initiate data transfers and access support and other tools and services offered by BioMedIT. BioMedIT network can be used by researchers from all Swiss universities, research institutes, hospitals, service providers and other interested partners. The following diagram illustrates the setup of the current BioMedIT network landscape.
Security Architecture in BioMedIT Network
Due to the sensitive nature of the data being processed in the BioMedIT network, the utmost priority is given to ensuring robust information security for all computational and data assets. To achieve this goal, a comprehensive set of security controls have been implemented across the network. Some of the key security controls implemented in the security architecture are as follows:
- Exhaustive local & global Information Security Policies
The BioMedIT network leverages from multiple layers of secure comprehensive guidelines and compliances.
- Hosting Institution Security Guidelines: Each hosting institution within the BioMedIT network follows its own set of security guidelines and policies. These guidelines are designed to uphold the institution's security standards and align with industry best practices. They form the initial layer of security for the data and infrastructure housed within the institution.
- BioMedIT Information Security Policy: The BioMedIT network has its own comprehensive Information Security Policy. This policy outlines the overarching security requirements for all nodes within the network. It covers various aspects of security, including data access, data transfer, encryption, authentication and authorization, and other relevant measures. This policy is tailored to meet the specific security needs of each node within the network.
- Node-specific Security Officers: Each node within the BioMedIT network is supported by a dedicated security officer. These security officers play a crucial role in enforcing and enhancing the security of the infrastructure. They have the authority to implement additional security measures as needed, ensuring that the overall security posture remains robust and aligned with the BioMedIT guidelines.
These three layers of security work in harmony, creating a robust and dynamic security framework for BioMedIT network. Security officers at each node continually assess and respond to potential threats, ensuring that the infrastructure remains secure while maintaining a user-friendly experience for all researchers. These efforts are carried out in full compliance with the BioMedIT guidelines and requirements. Through this multi-layered approach, the BioMedIT network guarantees the protection and confidentiality of sensitive data.
- Accessible only to bonafide users
BioMedIT covers all relevant aspects necessary to provide a secure computing infrastructure for sensitive data to researchers. Among the most important points is access management: defining and strictly controlling who gets access to the network. For this reason, only verified members of bonafide Swiss institutions can access BioMedIT services. In addition, access of BioMedIT services is only possible via bonafide research institutions which is further secured by two-factor authentication (2FA).
- Data transfer coordination
BioMedIT ensures secure transfer of data in and out of the network. Not only each transfer needs to be approved by the different parties involved (the BioMedIT node, the data provider and the BioMedIT Central), all transfer can only be realized using BioMedIT secure transfer tool (sett). This tool is used to encrypt data to transfer, to decrypt it (only by defined recipient) once it reaches the B-space and to establish a secure communication channel with the node where the research project is hosted.
- Secure B-Spaces
A researcher that uses the BioMedIT network has access to an isolated virtual environment where sensitive data can be processed. This environment is called a B-Space. Each project has a unique B-Space, which is separated on a network & virtualization level from all other B-Spaces and the rest of the infrastructure. B-Spaces could be only accessible via researcher’s organization’s network and connections to the internet is not possible either, however some specific web services such as BioMedIT GitLab, Container registry, BioMedIT Portal etc. could be accessible. Extensive logging of user actions inside B-Space is done to comply with auditing requirements for Data processors.
- BioMedIT Secure Software toolstack
In BioMedIT network, by default only official tools & software stacks from trusted software registries such as Compute Canada could be executed. These tools are kept up-to-date & patched to latest official versions for minimizing exploitation of security vulnerabilities. In case researchers want to bring in software tools developed by them these are subject to security reviews: via source code & container analyzer tools and a security review by BioMedIT security officers (if needed).
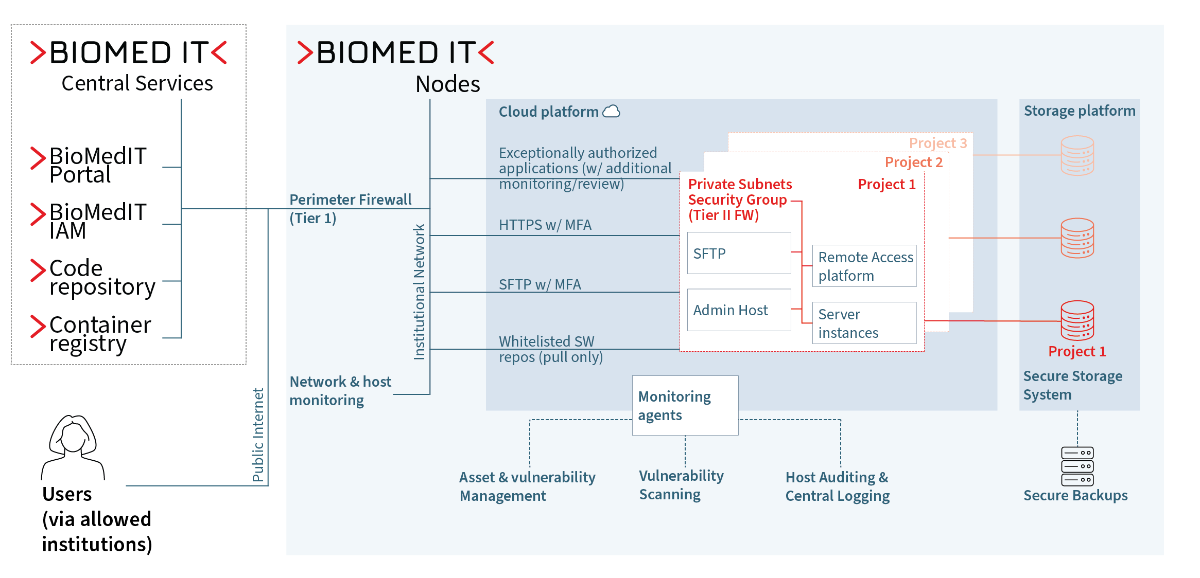
Node architecture
Every BioMedIT node provides similar services to its users and the actual infrastructure architecture may vary. However, logical architecture for security of data and computational assets are similar. In this section, we will discuss about node security architecture.
From the network perspective, a selection of commercial and open source tools provide network security monitoring. This capability depends on the architecture of the individual nodes, and will typically include network traffic monitoring, host intrusion detection, and dashboard and alerting capabilities. In cases where more detailed monitoring is necessary, custom rules are added depending on the technical capabilities of the node.
Each B-Space has its own dedicated VLAN, which can only be accessed through secure communication channels. Network traffic is isolated on several axes, such as from the internet, from the institutional network, and from the other B-spaces. Furthermore, all the default service components in the B-space are protected with MFA.
An actively maintained inventory of all assets is kept and scheduled vulnerability scanning of assets is performed.
The following diagram gives an overview of the logical security architecture for BioMedIT node.